Hi Soheb Khan,
You can create a group policy to deny the delete permission on the folder. Open Group Policy Management Editor, navigate to Computer Configuration / Policies / Windows Settings / Security Settings / File System and set the user permissions in the advanced permissions.
Best Regards,
Ian Xue
If the Answer is helpful, please click "Accept Answer" and upvote it.
Hi Soheb Khan,
You can create a group policy to deny the delete permission on the folder. Open Group Policy Management Editor, navigate to Computer Configuration / Policies / Windows Settings / Security Settings / File System and set the user permissions in the advanced permissions.
Best Regards,
Ian Xue
If the Answer is helpful, please click "Accept Answer" and upvote it.
I have the same question.
I got request from time to time that user need to restore folders/files on network shared drive by NetApp. I wonder if there is a way to prevent user from deleting/moving them.
Please help!
Thanks in advance!
Is there a software or tool to restrict users from deleting files and folder?
How to restrict users from deleting files and folders in Windows Server 2019
Protect files from being deleted
How do you restrict staff’s ability to create/delete/modify folders only in a shared drive but not the files?
Some ways to prevent deletion:
- Modify ownership of the folder.
- Right-clik the folder and select Properties.
- On the Security tab, select Advanced.
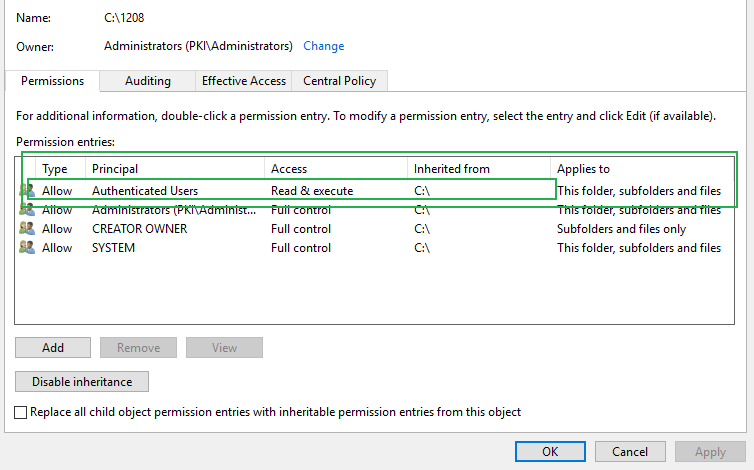
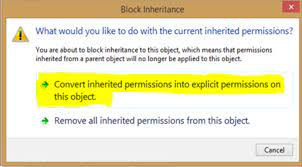
- On the Permissions tab, Disable inheritance, removing all inherited permissions.
- This denies permission to do anything to that folder, until you assign an owner and set permissions for that owner. Of course, that owner should be able to delete the folder... so you might want to create a new user for that purpose.
- Use third-party software, such as TunesBro Folder Unbreak or an alternative. N.B. Check reviews and use VirsuTtoal to look for malware before installing any software.
You can't delete a folder with a locked file in it. The trick is how to keep it open all the time. There are endless ways to do this.
One lightweight way to do this with built in methods would be a scheduled task that runs on boot that opens the files. You could make a hidden system file called something like .criticalFolderLock.cmd that is a script that runs forever.
For example, a script like this:
set lockFile=%userprofile%\Downloads\.criticalFolderLock.cmd
echo pause > %lockFile%
attrib +S +H %lockFile%
%lockFile%
NOTE: Change the path you want to lock open in the lockFile variable.
The only caveat is that this would keep a cmd window running in the background, to keep the file lock.
Hi there
I have been going through forum regarding restricting people from deleting the files. But dont think i have found any solution yet.
I have a windows server, and would like to restrict people from deleting the files. Using NTFS permissions i know we cannot as they cannot modify either.
So can someone shed me some light on 3rd party softwares or tools please?
Thanks
There is no such tool but you can restrict it by setting the permissions to authenticated users or everyone (Read and Write)
This old thread might be helpful for you Help me! how to prevent users deleting files/folders in 'SHARED NETWORK DRIVE'
BTW, you can audit/monitor such activities by using the Lepide File Server auditing solution.
In Windows a file generally gets its ACL from the folder in which it is created. If the folder allows non-owners of files to delete them, then they can even if the owner is an administrator.
As you note you can change this for a file, a folder or a folder tree.
To change for all folders you need to first identify which folder trees you want to change (e.g. you shouldn't start changing permissions of C:\Users, C:\Windows, ... and other system folders).
Then for each of these you need to modify the ACL. This can be done in code or script (e.g. PowerShell), but needs more time to write up than I have now (if you just want to copy one ACL to another folder you can get-acl on the first and then set-acl on the other).
However I would suggest you consider why you want to do this. If a user needs to create files that only they can delete the best route is to create a folder, with specific ACL, for that purpose. Not to make some global change so the administrator doesn't have to think.
When you make a folder as admin it and its contents apply a default security level that gives accounts in the Users group read and execute but not delete. I would agree with Richards comment rather than defining explicit permissions I would define what you want to do and make sure that the other user accounts use the proper user group. If you have other user accounts and they are in the administrator group they will be able to access any folders if they drill down to the file system as admin. Even if you set explicit permissions to one user account a user in the admin group can take ownership and then make any changes they want. Only a more limited account will prevent that.
I'm still having a problem with this. I understand the concept of permissions, but have not ever been able to use them effectively in Windows as it seems like the permissions are not mutually exclusive. I still wish Windows was a bit more like Unix in this regard. To summarize, I would like to eliminate the ability to delete or modify a photo, but still retain the ability to add tags.
My computer is set up with an Admin and a Std User account. I tried 3 things:
- Photo with Owner=Admin. I went into permissions and denied "write". From Std User account I am not able to add a tag, am not able to modify, but can still delete the file.
- Photo with Owner=Admin. I went into properties and selected "Read Only". Same response as above.
- Photo with Owner=Admin. I am able to modify the tag, but still able to delete.
It seems like option 3 above should be the closest that I can get, but I thought you could not delete a file that belonged to a different owner. Is this true? What am I doing wrong?
Perhaps a 3rd party app is my best bet, but I was hoping I could do it with Windows 7.
Thanks.
Any ideas? Please help.
I am trying to prevent users from accidentally deleting a certain folder in a parent folder, while still giving them modify permission on all other files and folders in the parent folder. But they should be also able to modify files and folders in this certain folder
Prevent Folder Deletion or inadvertent Drag and Drop with NTFS security
If you want to prevent a specific folder from being deleted or dragged and dropped elsewhere, even if it has elevated implicit permissions, you can set an explicit DENY to the FOLDER ONLY for the user account or security group which you want to prevent this action from being performed.
You can complete this folder security lock down using ICACLS with a local path (e.g C:\Path\FolderA\FolderE) or a UNC path (e.g \\server\share\FolderA\FolderE).
Example ICACLS syntax to run from an elevated command prompt
ICACLS "\\server\share\FolderA\FolderE" /deny "<UserOrGroupNameToDeny>":(DE)
Permissions Used
/deny user:permission
Explicitly deny the specified user access rights.
This will also remove any explicit grant of the
same permissions to the same user.
perm is a permission mask and can be specified in one of two forms:
a comma-separated list in parentheses of specific rights:
DE - delete
What this does
Running the above with those options in that syntax will set an explicit DENY to the NTFS DELETE permission on that FOLDER ONLY to that specific user account of security group.
You can confirm the deny permissions to the folder for the user account or security group by:
right-clickthe folder you've used in the command,- Select the Security tab,
- In the
Group or user name:area scroll to or select and highlight the account or group you've used in the command, - In the
Permissions for Administratorsarea you will see the NTFS permission attributes forAllowandDeny - You'll see a check mark in the
DENYcolumn of thespecial permissionsrow for the account or group you've used in the command

- Select Advanced and go to the Permissions tab
- Check for the
Name(orPrincipal) value that you used in command, forDENYin theTypefield - The
Permissions(orAccess) field should showDeleteand theApply to(orApplies to) will showthis folder only

NOTES
Please note that unchecking an ALLOW DELETE attribute is not the same as leaving that in place as-is and then creating a separate NTFS ACL rule for this same security group or user account saying to explicitly DENY the DELETE security.
This solution does NOT disallow DELETE this way
(WRONG)

This solution WILL explicitly DENY DELETE at this level to THIS FOLDER ONLY
(CORRECT)

(CORRECT)

Further Reading and Resources
- ICACLS
This is not possible. You can make a folder to not be able to be deleted by removing modifying rights, but that will cause all files in that folder to automatically get that same right, making it impossible for people to work on new files in that folder.
You can create subfolders and disable inheritance of rights to make people able to work in those folders, but you should move the remaining folders into a subfolder or decide against doing this.
You can also give files different rights than their parent folder, but that would only allow people to edit existing files, including deleting them. But when they want to copy or create a new file in this folder they can't.
Also, please note that the filesystem you're suggesting is bad practice. You'll want to set the permission on a as high level as possible, setting inheritance to all subfiles. The reason is, that you can push rights down to all child folders. If this is done from a higher folder, all rights are removed.
But sufficient to say, it is not possible to make it so that a folder cannot be deleted/moved while its content can. If deletion is of a great concern to you, enable Volume Shadow Copy and optionally a backup. If a folder is moved, it will be moved inside VSS also. If deleted, you can simply undelete from VSS (restore previous versions). If moving is of a concern and you can't find where it was moved to, make a daily backup and of course, you can always try to instruct people to simply not delete/move these folders.
This kind of action is usually because people simply are not aware they are not supposed to move them, and delete by accident can be undone using VSS.
Shared network drive. I have staff in one usergroup and managers in the other. I want to set it so staff can create, edit, rename files and folders but cannot delete them.
I have tried setting Deny 'Delete' but this doesn't let people rename files either (and only lets them create a file with a default file name)
Usually when I get a request for this, it's because someone was stupid and deleted or moved folders they shouldn't have.
Read and write requires Delete as well for things like renaming or editing. The only options are to limit staff/groups to read only, have a quick backup option (like shadow copies) or use an auditing tool like Netwrix' file server auditor.
Ahh the ol "I deleted the Z folder" or they basically fat fingered it and moved it under the "R" folder....
I wrote a powershell script to handle this.
PARAM (
[string]$path
)
##needs NTFSSecurity Module https://gallery.technet.microsoft.com/scriptcenter/1abd77a5-9c0b-4a2b-acef-90dbb2b84e85
Import-Module NTFSSecurity
foreach ($file in (Get-ChildItem $path)) {
if ($file.PSIsContainer -eq $true) {
Add-NTFSAccess $($file.fullname) -AccessRights Delete -Appliesto ThisFolderOnly -accesstype Deny -account everyone
get-ntfsaccess $($file.fullname)
}
}The key is that users can delete a file if the file's ACL entitles them to delete it or the containing directory's ACL gives them the delete-child permission. You need to make sure that this limited user doesn't get either permission. On the special folder from which they shouldn't be able to delete files, assign them the following permissions in the Advanced Security Settings window:
- Allow "traverse folder / execute file", "list folder / read data", "read attributes", "read extended attributes", "create files / write data", "create folders / append data", and "read permissions" on "this folder and subfolders"
- Deny "delete subfolders and files", "delete", and "change permissions" on "this folder, subfolders, and files"
- Allow full control on "files only" (this will be moderated by the previous deny rule)
But because this user is the owner of any files they create, they are entitled to change the permissions to allow deletion. The last piece of the puzzle is the arcane OWNER RIGHTS principal. You can type that phrase right into the user selection dialog where you would usually type the name of a user or group. Create one last rule on the folder that grants only "read permissions" on "subfolders and files only" to OWNER RIGHTS. Then the only advantage of being the owner of a file in that folder is that it guarantees ability to see the ACL, but not to change it.
Prevent NTFS Object Owners From Changing Permissions
If users access their data through a Windows network share, a system administrator can prevent the Owner of an NTFS file or folder from changing permissions by not granting the Full Control share permission:

Credit to this article for the concept.
Therefore, whatever permissions are granted to users in the first place will remain in effect, even for object owners, as they won't be able to exercise their ability as Owner to grant themselves permissions not permitted by the server administrator.